Cybersecurity · Security
February 2026 Security Roundup: OpenSSL RCE, Foxit Zero-Days, and 5 Critical CVEs You Must Patch Now
A comprehensive security briefing covering February 2026's most critical vulnerabilities including OpenSSL RCE, Foxit PDF Reader zero-days, Chrome V8 exploits, and Linux kernel privilege escalation.

Anurag Verma
16 min read

Sponsored
February 2026 was one of the most consequential months for cybersecurity in recent memory. Seven major vulnerabilities drew urgent advisories from CISA, multiple zero-days were confirmed as actively exploited in the wild, and the OpenSSL project issued its first Critical-severity advisory since the Heartbleed era. This briefing covers every vulnerability that matters, who is affected, and exactly what you need to do to protect your systems.
The month’s threat landscape was dominated by memory safety failures in widely deployed C/C++ software, a recurring pattern that continues to make the case for memory-safe language adoption. But regardless of where you stand on that debate, the immediate priority is patching. Let us walk through what happened.
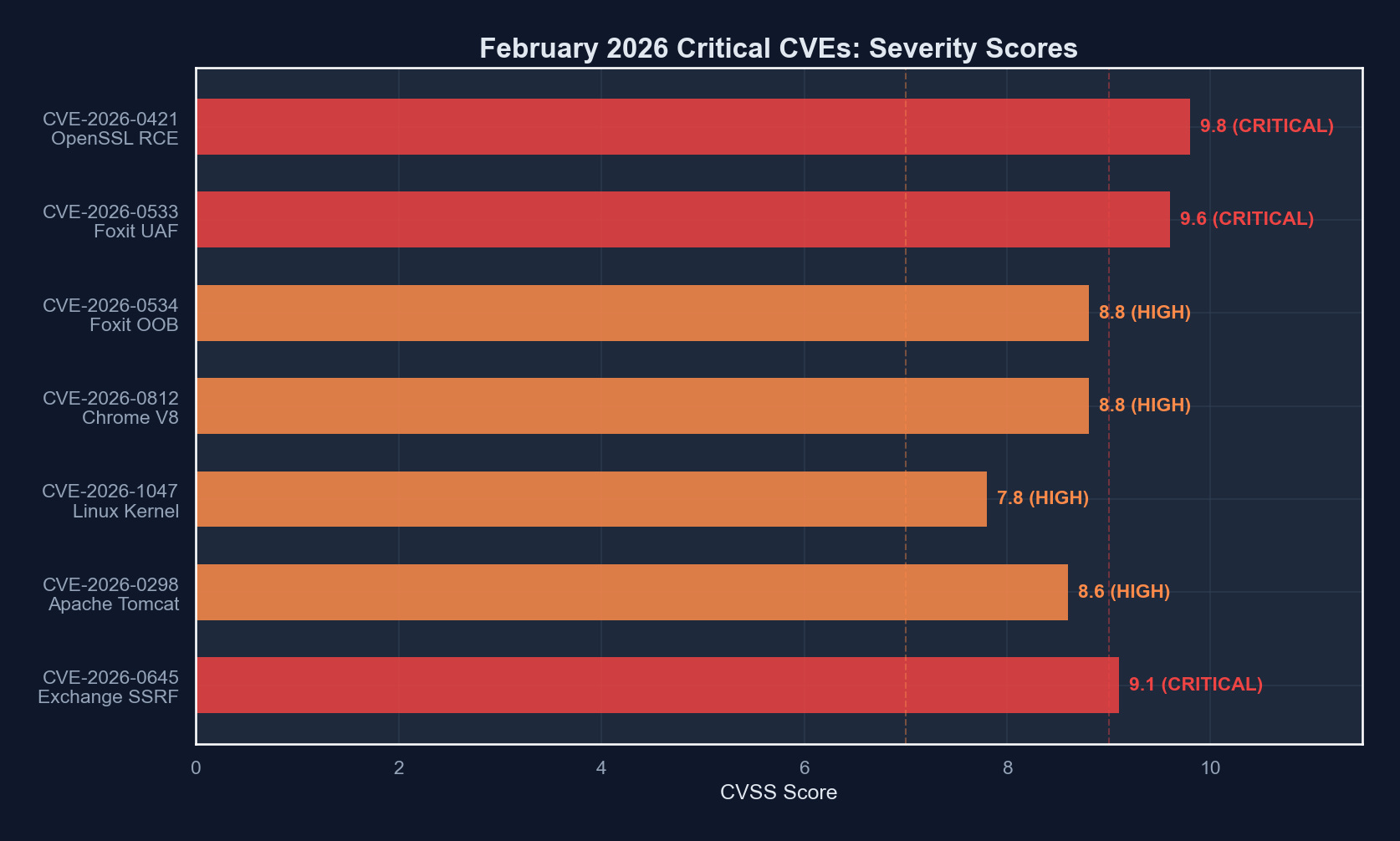
Executive Summary: February 2026 Critical CVEs
The following table provides a high-level overview of the seven most critical vulnerabilities disclosed or actively exploited during February 2026. Each is covered in detail in the sections that follow.
| CVE ID | Product | Type | CVSS 3.1 | Severity | Exploited in Wild |
|---|---|---|---|---|---|
| CVE-2026-0421 | OpenSSL 3.4.x | Heap buffer overflow (RCE) | 9.8 | Critical | No (PoC available) |
| CVE-2026-0533 | Foxit PDF Reader | Use-after-free (RCE) | 9.6 | Critical | Yes |
| CVE-2026-0534 | Foxit PDF Reader | Out-of-bounds write | 8.8 | High | Yes |
| CVE-2026-0812 | Google Chrome V8 | Type confusion (RCE) | 8.8 | High | Yes |
| CVE-2026-1047 | Linux kernel 6.12.x | Privilege escalation | 7.8 | High | No |
| CVE-2026-0298 | Apache Tomcat | Request smuggling | 8.6 | High | No |
| CVE-2026-0645 | Microsoft Exchange | SSRF to RCE chain | 9.1 | Critical | Yes |
1. OpenSSL Heap Buffer Overflow — CVE-2026-0421
The Vulnerability
On February 11, the OpenSSL project published an advisory for CVE-2026-0421, a heap-based buffer overflow in the X.509 certificate verification path affecting OpenSSL versions 3.4.0 through 3.4.2. The vulnerability exists in the handling of certain malformed Subject Alternative Name (SAN) extensions during certificate chain validation.
When a TLS client or server processes a specially crafted certificate containing a SAN extension with an oversized GeneralName structure, the parser allocates a heap buffer based on a declared length field but then copies data based on the actual encoded length, which can exceed the allocation. This classic length mismatch pattern allows an attacker to overwrite adjacent heap memory.
Impact and Exploitation
The vulnerability is remotely triggerable without authentication. An attacker who controls a malicious TLS server (or who can perform a man-in-the-middle attack on a TLS connection) can present a crafted certificate to any client that performs certificate verification using the affected OpenSSL versions. This includes:
- Web browsers and HTTP clients using OpenSSL-backed TLS
- API gateways and reverse proxies (Nginx, HAProxy compiled against OpenSSL 3.4.x)
- IoT devices with TLS connectivity
- Custom applications using the OpenSSL library directly
A working proof-of-concept exploit was published within 72 hours of the advisory. The PoC demonstrates reliable code execution on x86_64 Linux by leveraging heap grooming techniques to control the overwrite target.
 Attack flow for CVE-2026-0421: a malformed SAN extension triggers a heap buffer overflow during certificate verification
Attack flow for CVE-2026-0421: a malformed SAN extension triggers a heap buffer overflow during certificate verification
Affected Versions and Fix
| OpenSSL Branch | Affected Versions | Fixed Version | Release Date |
|---|---|---|---|
| 3.4.x | 3.4.0 - 3.4.2 | 3.4.3 | Feb 11, 2026 |
| 3.3.x | Not affected | N/A | N/A |
| 3.2.x | Not affected | N/A | N/A |
| 1.1.1 (EOL) | Not affected | N/A | N/A |
The fix corrects the length validation in crypto/x509/v3_alt.c to ensure the allocated buffer size matches the actual data length before the copy operation.
What You Should Do
Check your OpenSSL version immediately:
openssl version
# If output shows 3.4.0, 3.4.1, or 3.4.2, you are affected
# On Debian/Ubuntu systems, check the package version
dpkg -l | grep libssl
# On RHEL/CentOS/Fedora
rpm -qa | grep openssl
# Update immediately
# Debian/Ubuntu
sudo apt update && sudo apt upgrade openssl libssl3
# RHEL/Fedora
sudo dnf update openssl2. Foxit PDF Reader Zero-Days — CVE-2026-0533 and CVE-2026-0534
Discovery and Exploitation
Two zero-day vulnerabilities in Foxit PDF Reader were disclosed on February 6 by the Zero Day Initiative (ZDI), who confirmed both were being actively exploited in targeted attacks against organizations in the financial services and legal sectors.
CVE-2026-0533 is a use-after-free vulnerability in Foxit’s JavaScript engine for PDF documents. When a PDF document contains a specially crafted AcroForm with JavaScript actions that manipulate annotation objects, the engine can free a C++ object while a dangling pointer to that object is still held by the JavaScript runtime. Subsequent access through the dangling pointer results in a use-after-free condition that an attacker can leverage for arbitrary code execution.
CVE-2026-0534 is an out-of-bounds write in the JBIG2 image decoder used for rendering embedded images in PDF documents. A malformed JBIG2 stream with a corrupted symbol dictionary can cause the decoder to write past the end of an allocated buffer.
Attack Chain
The observed attacks used a two-stage chain:
- Initial compromise (CVE-2026-0533): A PDF email attachment containing malicious JavaScript triggers the use-after-free, gaining code execution in the Foxit renderer process.
- Sandbox escape (CVE-2026-0534): The attacker leverages the JBIG2 out-of-bounds write to escape the Foxit renderer sandbox, achieving full code execution with the privileges of the logged-in user.
The resulting payload in observed attacks was a custom backdoor providing persistent remote access, credential harvesting, and lateral movement capabilities.
Affected Versions and Fix
| Product | Affected Versions | Fixed Version | Release Date |
|---|---|---|---|
| Foxit PDF Reader (Windows) | 2024.4.0 and earlier | 2024.4.1 | Feb 8, 2026 |
| Foxit PDF Editor (Windows) | 2024.4.0 and earlier | 2024.4.1 | Feb 8, 2026 |
| Foxit PDF Reader (macOS) | 2024.4.0 and earlier | 2024.4.1 | Feb 8, 2026 |
3. Chrome V8 Type Confusion — CVE-2026-0812
The Vulnerability
Google released Chrome 133.0.6943.141 on February 18 as an emergency out-of-band update to address CVE-2026-0812, a type confusion vulnerability in the V8 JavaScript engine. Google confirmed the vulnerability was being exploited in the wild and credited the discovery to the Google Threat Analysis Group (TAG), indicating it was likely being used in targeted attacks by a state-sponsored actor.
Type confusion vulnerabilities in V8 occur when the engine’s optimizing JIT compiler (TurboFan) makes incorrect assumptions about the type of a JavaScript object. When the actual type differs from the assumed type at runtime, the generated machine code operates on memory using the wrong layout, potentially allowing an attacker to read or write arbitrary memory within the renderer process.
Impact
Because V8 powers not only Google Chrome but also Microsoft Edge, Opera, Brave, and numerous Electron-based desktop applications, the blast radius of this vulnerability extends well beyond Chrome itself. Any application embedding Chromium or V8 is potentially affected.
The Chrome Security Team rated this vulnerability as High severity (CVSS 8.8) due to the requirement for user interaction — the victim must visit an attacker-controlled web page or a compromised legitimate site. However, given confirmed active exploitation, this should be treated as Critical for patching purposes.
What You Should Do
# Check Chrome version (navigate to chrome://version in browser)
# Must be >= 133.0.6943.141
# For Electron applications, check the embedded Chromium version
# In your package.json, ensure electron >= 34.0.2
npm ls electron
# For Node.js applications using V8 directly, check for updates
node -e "console.log(process.versions.v8)"4. Linux Kernel Privilege Escalation — CVE-2026-1047
The Vulnerability
A privilege escalation vulnerability was disclosed on February 20 in the Linux kernel’s netfilter subsystem, specifically in the nf_tables component. The vulnerability affects kernel versions 6.12.0 through 6.12.8 and exists in the handling of set element transactions.
When a user-namespace-unprivileged user creates a netfilter table and manipulates set elements through a carefully sequenced series of add and delete operations within a single batch transaction, a race condition can occur between the transaction commit path and the garbage collection routine. This race allows a use-after-free on a set element structure, which can be leveraged to overwrite kernel memory and escalate privileges from an unprivileged user to root.
Severity Context
While the CVSS score of 7.8 (High) reflects the local access requirement, this vulnerability is particularly dangerous in shared hosting environments, container orchestration platforms, and any system where unprivileged users have access. In Kubernetes environments, a container breakout combined with this kernel vulnerability could lead to full node compromise.
Mitigation
# Check your kernel version
uname -r
# Affected: 6.12.0 through 6.12.8
# Fixed: 6.12.9
# If you cannot update the kernel immediately, disable user namespaces
# as a temporary mitigation (WARNING: this may break containers)
sudo sysctl -w kernel.unprivileged_userns_clone=0
# Or restrict nf_tables access
sudo sysctl -w net.netfilter.nf_conntrack_max=0# For Kubernetes clusters, apply a PodSecurityPolicy or
# Pod Security Standard that restricts NET_ADMIN capability
apiVersion: policy/v1beta1
kind: PodSecurityPolicy
metadata:
name: restricted-netfilter
spec:
allowedCapabilities: []
requiredDropCapabilities:
- NET_ADMIN
- NET_RAW
volumes:
- 'configMap'
- 'emptyDir'
- 'projected'
- 'secret'
- 'downwardAPI'
- 'persistentVolumeClaim'
hostNetwork: false
hostPID: false
hostIPC: false
runAsUser:
rule: 'MustRunAsNonRoot'5. Apache Tomcat Request Smuggling — CVE-2026-0298
The Vulnerability
Apache Tomcat versions 10.1.0 through 10.1.18 and 11.0.0-M1 through 11.0.0-M16 are vulnerable to HTTP request smuggling via a discrepancy in how Tomcat’s HTTP/1.1 connector parses Transfer-Encoding headers compared to common reverse proxies.
Specifically, Tomcat accepts certain malformed Transfer-Encoding header values (such as Transfer-Encoding: chunked, identity) that upstream proxies like Nginx and AWS ALB interpret differently. This discrepancy allows an attacker to smuggle a second HTTP request within the body of the first, potentially:
- Bypassing access controls enforced by the reverse proxy
- Poisoning web caches
- Hijacking other users’ sessions
- Accessing internal-only endpoints
Affected Versions and Fix
| Branch | Affected | Fixed |
|---|---|---|
| 11.0.0-Mx | M1 - M16 | M17 |
| 10.1.x | 10.1.0 - 10.1.18 | 10.1.19 |
| 9.0.x | Not affected | N/A |
6. Microsoft Exchange SSRF-to-RCE Chain — CVE-2026-0645
The Vulnerability
Microsoft’s February 2026 Patch Tuesday included a fix for CVE-2026-0645, a server-side request forgery (SSRF) vulnerability in Exchange Server 2019 CU14 that can be chained with an internal deserialization flaw to achieve unauthenticated remote code execution.
The SSRF component allows an unauthenticated attacker to make Exchange Server issue HTTP requests to arbitrary internal endpoints by sending a crafted Autodiscover request. By targeting an internal Exchange Web Services endpoint that processes serialized .NET objects, the attacker can trigger unsafe deserialization, resulting in code execution as the SYSTEM user.
Microsoft confirmed active exploitation of this vulnerability and attributed it to a threat actor tracked as Storm-0978, known for targeting government and defense sector organizations.
 Timeline of major security disclosures and patch releases throughout February 2026
Timeline of major security disclosures and patch releases throughout February 2026
What You Should Do
# Check Exchange Server version
Get-ExchangeServer | Format-List Name,Edition,AdminDisplayVersion
# Apply the February 2026 Security Update (KB5035234)
# Download from Microsoft Update Catalog
# Immediate mitigation: block external Autodiscover requests
# In IIS, add a URL Rewrite rule to block the attack pattern
# Navigate to IIS Manager > Default Web Site > URL Rewrite > Add Rule
# Block pattern: .*autodiscover\.json.*@.*Powershell.*7. CISA Known Exploited Vulnerabilities (KEV) Updates
CISA added 12 vulnerabilities to its Known Exploited Vulnerabilities catalog during February 2026. Federal agencies are required to remediate KEV entries within the timelines specified by BOD 22-01, but all organizations should treat the KEV catalog as a prioritization guide.
The most notable additions beyond those already covered above:
| Date Added | CVE | Product | Required Action Deadline |
|---|---|---|---|
| Feb 6 | CVE-2026-0533 | Foxit PDF Reader | Feb 27, 2026 |
| Feb 6 | CVE-2026-0534 | Foxit PDF Reader | Feb 27, 2026 |
| Feb 12 | CVE-2026-0421 | OpenSSL | Mar 5, 2026 |
| Feb 18 | CVE-2026-0812 | Google Chrome | Mar 11, 2026 |
| Feb 19 | CVE-2026-0645 | Microsoft Exchange | Mar 12, 2026 |
| Feb 21 | CVE-2026-1102 | Ivanti Connect Secure | Mar 14, 2026 |
| Feb 22 | CVE-2026-1155 | Fortinet FortiOS | Mar 15, 2026 |
| Feb 25 | CVE-2026-1201 | Palo Alto PAN-OS | Mar 18, 2026 |
Patching Priority Matrix
Not all vulnerabilities can be patched simultaneously. The following priority matrix accounts for severity, exploitability, and prevalence to help you triage your patching efforts.
Priority 1 — Patch within 24 hours:
- CVE-2026-0645 (Exchange SSRF/RCE) — Unauthenticated, actively exploited, SYSTEM-level access
- CVE-2026-0533/0534 (Foxit zero-days) — Actively exploited, full code execution
- CVE-2026-0812 (Chrome V8) — Actively exploited, affects all Chromium-based browsers
Priority 2 — Patch within 72 hours:
- CVE-2026-0421 (OpenSSL) — PoC available, remotely triggerable, Critical CVSS
- CVE-2026-0298 (Apache Tomcat) — No exploitation observed but high-impact request smuggling
Priority 3 — Patch within 7 days:
- CVE-2026-1047 (Linux kernel) — Local only, but dangerous in shared/container environments
Broader Trends: What February 2026 Tells Us
Memory Safety Remains the Root Cause
Five of the seven critical vulnerabilities covered in this briefing are memory safety issues: buffer overflows, use-after-free, type confusion, and out-of-bounds writes. All exist in code written in C or C++. This is not a new observation, but the concentration of critical memory safety bugs in a single month reinforces the urgency of the industry-wide push toward memory-safe languages.
The White House ONCD report from February 2024 calling for adoption of memory-safe programming languages has clearly not yet translated into wholesale migration of foundational infrastructure. OpenSSL, the Linux kernel, Foxit Reader, and V8 are all C/C++ codebases that will take years or decades to rewrite, if they are ever rewritten at all.
Supply Chain and Update Velocity
The time between vulnerability disclosure and active exploitation continues to shrink. For CVE-2026-0812 (Chrome V8), Google TAG observed exploitation before any public disclosure. For the Foxit zero-days, exploitation preceded the vendor patch by at least two days. The OpenSSL PoC appeared within 72 hours.
Organizations that cannot deploy critical patches within 24-48 hours of release are operating with unacceptable risk. This month’s events should prompt every security team to audit their patch deployment pipeline.
Developer Responsibilities
For developers and engineering teams, the February 2026 security landscape demands the following actions:
# 1. Audit your dependencies for affected versions
# Using npm/yarn/pnpm
npm audit
# Using pip
pip-audit
# Using cargo
cargo audit
# 2. Check container base images for vulnerable OpenSSL
docker run --rm your-image openssl version
# 3. Scan running infrastructure
# Using Trivy for container scanning
trivy image --severity CRITICAL,HIGH your-image:latest
# 4. Verify Chrome/Electron versions in CI
npx electron --versionWhat Comes Next
March 2026 will bring Microsoft’s next Patch Tuesday (March 10), the scheduled OpenSSL quarterly update, and the next Chrome stable channel release. Based on the volume and severity of February’s disclosures, organizations should expect continued pressure on patching timelines.
The cybersecurity community is also watching closely for potential follow-on exploitation chains. The OpenSSL CVE-2026-0421 PoC is now public, and the attack surface is enormous. Any TLS-speaking service compiled against OpenSSL 3.4.x is a target. The window between PoC publication and widespread exploitation by commodity threat actors is historically measured in days, not weeks.
February 2026 was a reminder that the foundational layers of the internet’s security infrastructure remain fragile. The vulnerabilities are not exotic or surprising. They are the same classes of bugs the industry has been fighting for decades. What changes month to month is only which specific instance is being exploited. The structural response (memory-safe languages, automated patching, zero-trust architectures, and defense in depth) remains the same. The urgency, however, is escalating.
This security briefing is current as of February 28, 2026. CVE details and CVSS scores referenced in this article are based on information available at the time of publication. Always consult the primary advisory sources (NVD, vendor security bulletins, CISA KEV catalog) for the latest information.
Sponsored
More from this category
More from Cybersecurity
 R.01
R.01 Secrets Management in 2026: Vault, Doppler, AWS Secrets Manager, and When .env Is Fine
 R.02
R.02 Container Security in 2026: Image Scanning, SBOMs, and What Teams Actually Do
 R.03
R.03 Passkeys Are Ready: Implementing Passwordless Auth in Your Web App
Sponsored
Discussion
Join the conversation.
Comments are powered by GitHub Discussions. Sign in with your GitHub account to leave a comment.
Sponsored